I recently got a bank account with a local credit union. This week they sent me what I can only describe as what amounts to a very good phishing email for their own online banking service. I had to stop in my tracks as I looked at it, as I couldn’t quite believe it. I’m anonymizing the details of the credit union and domains in question as I’ve already sent them some comments as to why this is a bad idea and gotten some positive feedback from their VP of remote services. Try getting that kind of response (or any response) from a larger bank! One of the reasons why credit unions are better than larger banks.
Let’s take a closer look at this “phish”.
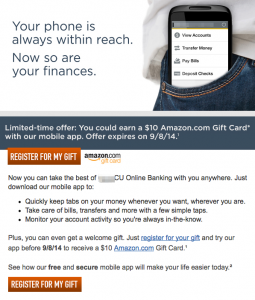
At first glance the email was a slick HTML branded email from “YCU” or Your Credit Union. It was touting their mobile banking application and as a limited-time offer they would give me a $10 Amazon gift card if I tried their app. It extolled me to click a button labeled “register for my gift.” Limited time offer. Free gift card. My phishing alarm bells were going off like crazy. I checked the headers.
Sender: [email protected]
From: “YCU”
<[email protected]>
The headers contained a valid SPF sender, but the domain was not the domain of my credit union, although it was very similar. My credit union was at yourcu.org not at yourcuob.org. Uh oh, this was looking like a definite phishing attack and a pretty good looking one at that.
The link included in the email appeared to be a long tracking URL of the kind you commonly find in email marketing messages. The company at this URL seemed to be a legitimate company providing online banking software, mobile app development, hosting, and marketing to financial institutions. Hmmm, the plot thickens. I wanted to follow the URL in a safe environment to see where it would go, so I loaded up a non persistent Linux VM and ended up landing on a yourcuob.org webpage asking for my name and email address associated with my YCU online banking account. Providing a name and email address presented you with a page with links to the Apple appstore, Google play store, and Amazon appstore for what looked like a genuine YCU app. Also on the page were instructions to download the app and login to your account from the app in order to be eligible for the gift card.
The main page of the yourcuob.org website redirected to yourcu.org. I decided to compare their WHOIS entries. First the entry for yourcu.org:
Domain Name:YOURCU.ORG
Creation Date: 1995-11-06
Updated Date: 2014-11-06
Registry Expiry Date: 2017-11-06
Sponsoring Registrar:Network Solutions, LLC
Registrant Name:PERFECT PRIVACY, LLC
Registrant Organization: Your Credit Union
Registrant Street: 12808 Gran Bay Parkway West
Registrant City:Jacksonville
Registrant State/Province:FL
Registrant Postal Code:32258
Registrant Country:US
Registrant Phone:+1.5707088780
Registrant Phone Ext:
Registrant Fax:
Registrant Fax Ext:
Registrant Email: [email protected]
YCU has been around online for a little while, although strangely they are using a private registration feature offered by network solutions. Let’s check yourcuob.org:
Domain Name:YOURCUOB.ORG
Creation Date: 1999-11-26
Updated Date: 2014-08-14
Registry Expiry Date: 2014-12-26
Sponsoring Registrar:MarkMonitor Inc.
Registrant Organization: Your Credit Union
Well this domain has been around for awhile and is registered with Mark Monitor which really continues to point us to the possibility this is actually a legitimate email. The technical contact in the WHOIS results also lists the same California based financial software and services company mentioned earlier and the website is hosted from IP space that also belongs to them.
So after all that work, it does appear this was actually a legitimate email from my credit union. I contacted them to confirm. My credit union obviously purchases software and services from this third party who is using this secondary domain to host this marketing campaign advertising their mobile app. I can only assume yourcuob.org stands for Your Credit Union Online Banking.
I hope in the future they realize how this campaign in general and this email in specific is sending the wrong message to their customers. Their customers should know not to follow links in emails that are not actually from the yourcu.org domain promising a free gift if they “click here”. Anyone could register a similar domain name, craft a phishing email using the YCU branding, host a malicious website that drops malware or asks for personal information in exchange for a promised gift card, and even write a malicious mobile app to collect credentials or worse.
And that’s the story of my bank’s phishing campaign.